Claim & start
< Back to blog
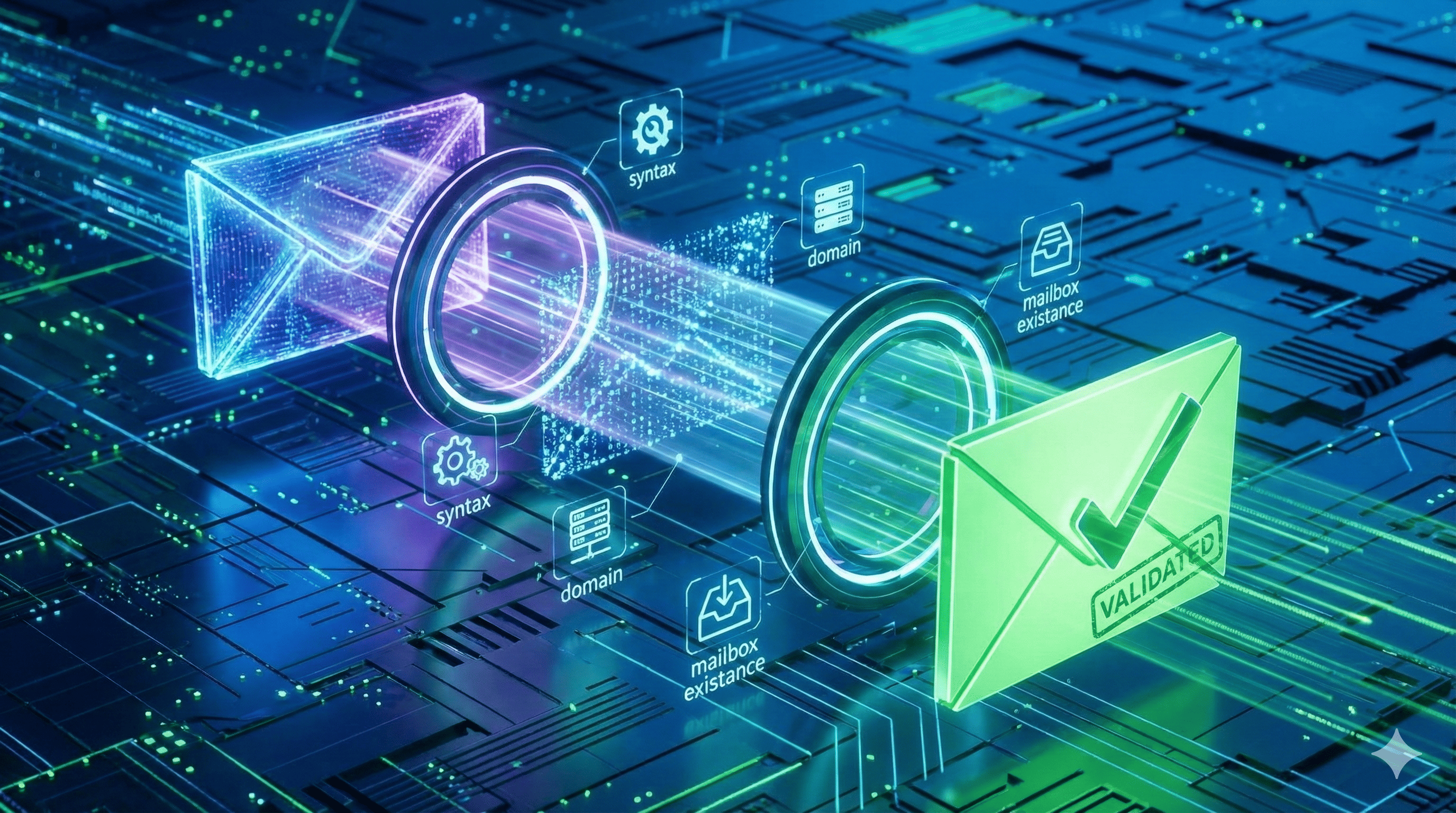
How Does Email Validation Work? The Mechanics of Verification
Uploading a raw database into an email validation tool and getting a pristine list back in minutes feels like magic. But behind the progress bar lies a highly complex sequence of network operations. Discover exactly how does email validation work, from basic syntax filtering and DNS record lookups to deep SMTP server handshakes and real-time threat detection.
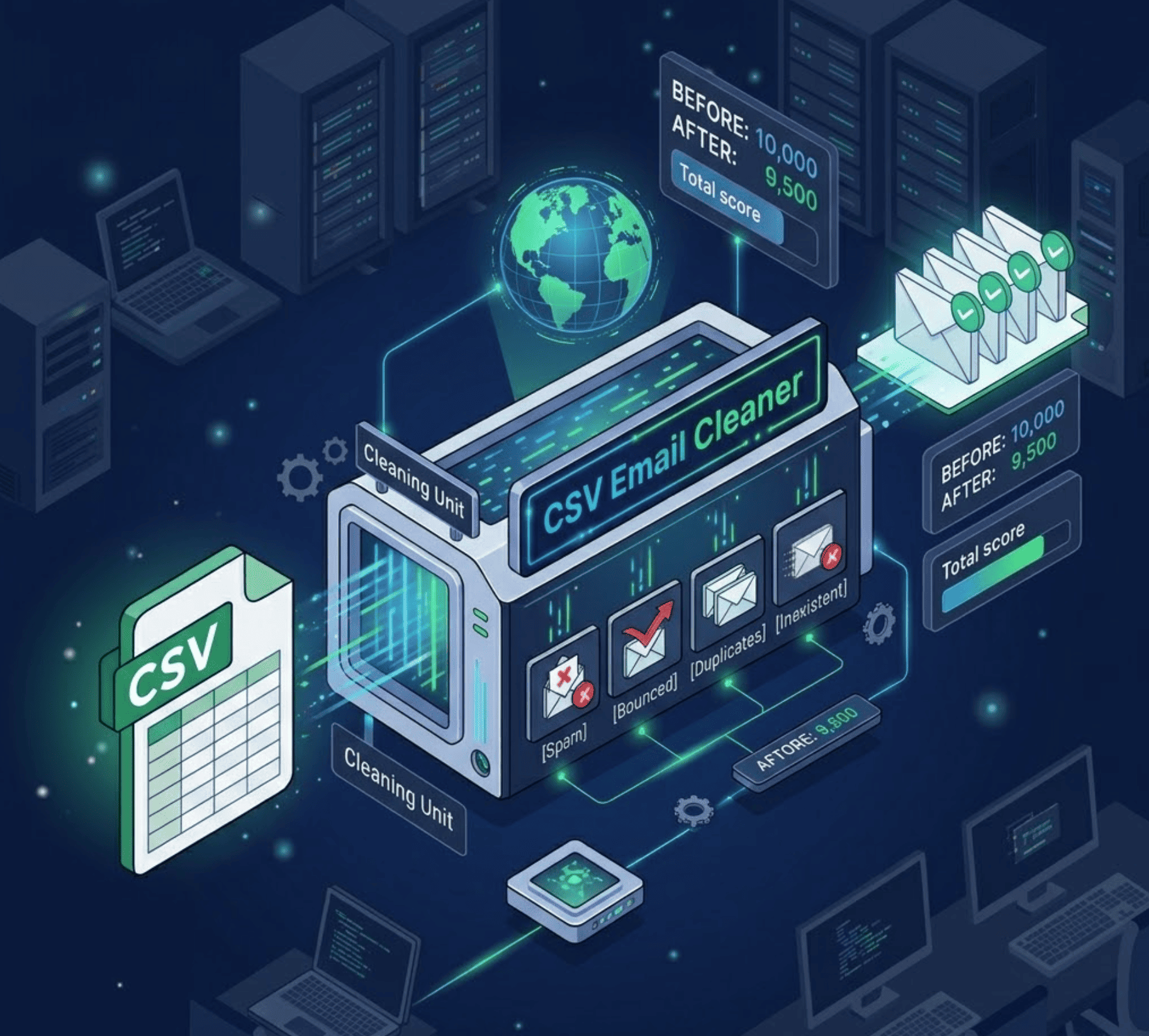
Uploading a raw, messy CSV file of 10,000 contacts into an email validation tool and getting a pristine, deliverable list back in just a few minutes feels a bit like magic. To the average marketer or sales professional, it is just a progress bar that ensures their next campaign will be a success.
But behind that simple user interface, an incredibly complex sequence of network operations is taking place.
To give you accurate results, the software must communicate with thousands of different mail servers across the globe simultaneously. It has to navigate strict corporate firewalls, bypass rate limits, and negotiate with anti-spam protocols—all without actually sending a single email payload to the end user.
If you are evaluating software to clean your database, or if you are an engineer wondering if you can just build this logic internally, you need to understand the underlying mechanics. In this guide, we are going completely under the hood to answer exactly how does email validation work, detailing the four-step technical process that protects your sender reputation.
Key Takeaways (TL;DR)
- The Definition: Email validation is the automated process of checking an email address for typos, active domain configurations, and real user inboxes to ensure a message can be successfully delivered.
- The 4-Step Process: A premium email verification tool runs every address through a syntax check, a DNS/MX record lookup, a deep SMTP handshake, and a final threat intelligence scan.
- No Emails Are Sent: The most crucial part of the process is the SMTP handshake, where the tool connects to the receiving server to ask if the user exists, but disconnects right before sending a message payload.
- Infrastructure is Key: Attempting to run this process from a standard application server will result in your IP address being blacklisted.
What Is Email Validation? (Validation vs. Verification)
Before we dive into the server architecture, it helps to answer a foundational question: what is email validation, and is it different from verification?
In the industry, these terms are often used interchangeably, but technically, they represent different stages of the process:
- Validation typically refers to checking the formatting and rules of the address. It asks, "Is this string of text shaped like a valid email?"
- Verification is the mechanical process of contacting the internet to confirm existence. It asks, "Does this mailbox actually exist on a real server right now?"
A modern, enterprise-grade platform performs both of these functions seamlessly in a fraction of a second. Here is the exact chronological process it follows.
How Does Email Validation Work? The 4-Step Process
When you submit an email address (like john.doe@company.com) to an API or bulk cleaning platform, it runs through an escalating series of filters. If the email fails at any step, the process stops immediately to save computing resources.
Step 1: Syntax and Formatting (The Regex Check)
The very first thing the software does is look for obvious human errors. It runs the text through a complex Regular Expression (Regex) to ensure it complies with standard formatting rules.
- It removes accidental spaces.
- It checks for the mandatory @ symbol.
- It ensures there are no illegal special characters.
While this step is incredibly fast, we know that Regex for Email Validation is not enough. Just because an email is typed correctly does not mean the inbox is real.
Step 2: Domain and DNS Verification (The MX Check)
If the syntax is correct, the tool must confirm that the domain (company.com) actually exists and is configured to receive mail.
The software queries the global Domain Name System (DNS) and asks for the domain's MX (Mail Exchanger) records. If a domain does not have an MX record, it is physically impossible for it to receive an email. If the user typed @gnail.com instead of @gmail.com, the MX lookup will fail, and the software will immediately flag the email as invalid, preventing a costly hard bounce.
Step 3: The SMTP Handshake (Pinging the Inbox)
This is the core engine of the process. If the domain has an active mail server, the software must connect to it to see if john.doe actually has an account there.
Using the Simple Mail Transfer Protocol (SMTP), the validation tool initiates a conversation with the receiving server on Port 25.
- Connect: The tool knocks on the server's door.
- Hello (HELO): The tool identifies itself.
- The Question (RCPT TO): The tool says, "I have a message for john.doe. Does he live here?"
If John Doe was fired last week and his account was deleted, the server responds with a 550 User Unknown error. The tool records this as a Hard Bounce. If the account is active, the server responds with a 250 OK code. Before the server expects the actual body of the email to be transmitted, the tool immediately drops the connection. We get the confirmation we need without ever sending a real message to the user.
Engineering Note: Attempting to build your own SMTP pinging script and running it from a standard application server is the fastest way to get your company's IP address blacklisted. Major providers like Google will flag thousands of disconnected SMTP handshakes as a "Directory Harvest Attack." To avoid severe deliverability penalties, developers route these checks through dedicated, rotating proxy networks like the EmailAwesome API.
Step 4: Advanced Threat Detection (The Intelligence Layer)
Pinging the server is not the final step. Just because an inbox exists does not mean it is safe to send to. The software runs the address through a final intelligence check:
- Catch-All Detection: Is the server configured to accept everything, making the ping unreliable? (Learn how to handle these in our Catch-All Email Guide).
- Disposable Emails: Is this a temporary burner account designed to bypass your signup forms?
- Spam Traps: Is this a known honeypot address created by internet service providers to catch spammers? (See our guide on Spam Trap Removal).
Why You Need a Dedicated Email Verification Tool
Now that you understand the mechanics, it becomes clear why implementing this technology is non-negotiable for modern businesses. Whether you are doing outbound B2B sales or running a SaaS application, protecting your database is vital.
You generally need to apply this technology in two ways:
- Bulk List Cleaning: Uploading your legacy CRM lists or freshly acquired lead databases to scrub dead accounts and spam traps before you launch a marketing campaign.
- Real-Time API Integration: Connecting an email verification tool directly to your website's signup forms so that typos and disposable emails are blocked dynamically before they ever enter your system.
By relying on specialized infrastructure to handle the heavy lifting, you ensure your sender reputation stays pristine, your analytics stay accurate, and your messages always reach the primary inbox.
Ready to see this powerful infrastructure in action? Get your API key and start your free scan with EmailAwesome today.
Table of contents
Written by
Frequently Asked Questions
Check the most Frequently Asked Questions
What is email validation?
How long does the email validation process take?
What is an SMTP handshake in email verification?
What is the difference between email validation and verification?
Does email validation improve my sender deliverability?