Claim & start
< Back to blog
SPF, DKIM, and DMARC Explained: The Ultimate Email Authentication Guide
Are your cold emails landing in the spam folder? Mailbox providers block unverified senders to stop phishing and spoofing. Master the "Deliverability Holy Trinity"—SPF, DKIM, and DMARC—with this comprehensive technical guide to authenticate your domain and guarantee inbox placement.

If your cold outreach campaigns are landing in the spam folder, your copy is likely not the problem. Your digital identity is.
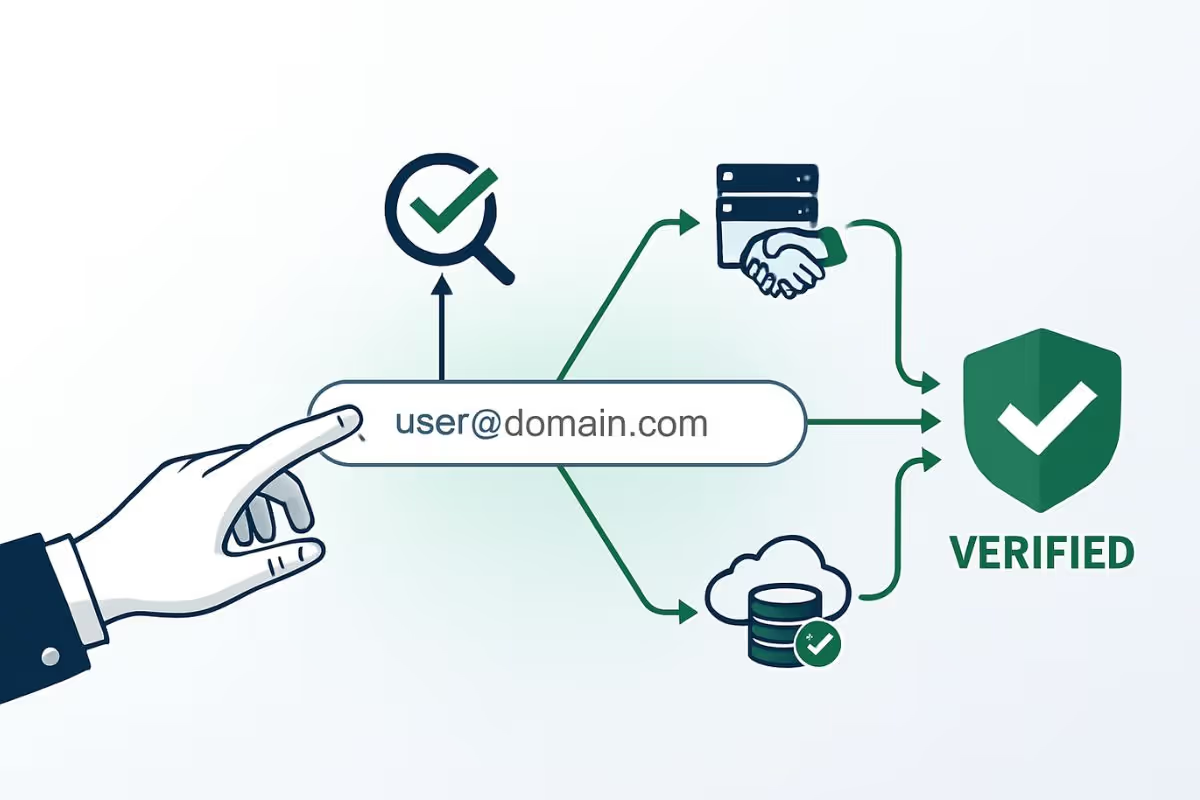
Every time you send an email, receiving mail servers (like Google Workspace, Microsoft 365, and Yahoo) act as security bouncers. They scan your email's invisible headers to answer one critical question: "Is this sender truly who they claim to be, or is this a hacker spoofing their domain?"
If you cannot cryptographically prove your identity, you will be blocked. Following the strict Google and Yahoo email sender requirements, anonymous mass emailing is officially dead.
To guarantee inbox placement, you must master the "Deliverability Holy Trinity": SPF, DKIM, and DMARC. Here is the complete technical breakdown of what they are, how they work together, and how to set them up.
What is SPF? (Sender Policy Framework)
The Analogy: Think of SPF as the VIP guest list at an exclusive club.
SPF is a standard DNS (Domain Name System) TXT record. It publicly lists all the IP addresses and third-party services (like Lemlist, Mailchimp, or Google Workspace) that are officially authorized to send emails on behalf of your domain.
When a receiving server gets an email from @yourcompany.com, it checks your domain's SPF record. If the IP address sending the email is on the list, it passes. If it isn't, the email is flagged as a forgery.
Example SPF Record:v=spf1 include:_spf.google.com include:mailgun.org ~all
v=spf1identifies the record type.include:specifies the authorized sending platforms.~all(Soft Fail) tells the receiver to accept emails from unauthorized IPs but mark them as suspicious.-all(Hard Fail) tells them to reject unauthorized emails entirely.
What is DKIM? (DomainKeys Identified Mail)
The Analogy: Think of DKIM as a wax seal on a physical envelope.
While SPF verifies where the email came from, DKIM verifies that the content of the email was not tampered with while in transit.
DKIM uses asymmetric cryptography. Your sending platform generates a private key (which it uses to mathematically sign every outgoing email) and a public key (which you publish in your DNS records). When the receiving server gets your email, it uses your public DNS key to decrypt the signature. If the math matches, the wax seal is unbroken, and the email is authentic.
Example DKIM Record:It usually looks like a long string of random characters published as a TXT or CNAME record under a specific selector:selector1._domainkey.yourcompany.com IN TXT "v=DKIM1; k=rsa; p=MIGfMA0GCSqGSIb..."
What is DMARC? (Domain-based Message Authentication, Reporting, and Conformance)
The Analogy: Think of DMARC as the manager who enforces the rules.
SPF and DKIM are excellent protocols, but what happens if an email fails one of those checks? Without DMARC, the receiving server just has to guess whether to deliver it or delete it.
DMARC ties SPF and DKIM together. It is a DNS policy that tells mailbox providers exactly what to do with messages that fail authentication. Furthermore, it sends XML reports back to you, so you can see who across the internet is attempting to spoof your domain.
DMARC Enforcement Levels:When setting up your DMARC TXT record, you must define a policy (p=):
p=none: The monitoring phase. Deliver the email normally, but send a report if it fails.p=quarantine: Send emails that fail authentication straight to the spam folder.p=reject: The ultimate protection. Completely block and delete any email that fails authentication.
Example DMARC Record:v=DMARC1; p=quarantine; rua=mailto:security@yourcompany.com; pct=100;
The Fatal Paradox: Why Authentication is Not Enough
Here is a devastating truth that most B2B marketers learn the hard way: You can have a perfect 10/10 technical setup, pass SPF, DKIM, and DMARC, and still get your domain permanently blacklisted.
Why? Because authentication only proves who you are. It does not prove that you are a good sender.
If you authenticate your domain and then blast an outdated CSV file full of dead emails, you are essentially providing cryptographic proof that you are a spammer. You will generate a massive spike in hard bounces, and ISPs will penalize your authenticated domain instantly.
Before you leverage your newly authenticated infrastructure, you must deploy an impenetrable data shield. You must run your lead lists through a deep email validation process like EmailAwesome.
By integrating an enterprise-grade validation API, you ensure that you never send an authenticated email to:
- Dead Inboxes: Understand the difference between a hard bounce vs soft bounce and eliminate non-existent addresses to keep your bounce rate under 1%.
- Hidden Honeypots: Prevent global blacklisting by learning what a spam trap is and letting EmailAwesome automatically filter them out.
- Risky Servers: Safely identify and segment catch-all email domains before they damage your sender score.
Setting up SPF, DKIM, and DMARC gives you the key to the inbox. Validating your data with EmailAwesome ensures they never change the locks on you.
If you have already damaged your domain by sending unverified emails, pause your campaigns immediately and follow our technical guide to fix your email sender reputation.
Table of contents
Written by
Frequently Asked Questions
Check the most Frequently Asked Questions
Do I need all three protocols (SPF, DKIM, and DMARC)?
How do I know if my SPF, DKIM, and DMARC are working?
Can I have multiple SPF records?
Where do I install these records?