Claim & start
< Back to blog
Why Regex for Email Validation Is Not Enough (The Limits of Syntax)
If you are searching for the perfect regex for email validation, you are solving the wrong problem. While regular expressions are great for catching basic typos, they cannot tell if an inbox actually exists. Discover why relying solely on syntax checks leaves your database vulnerable to hard bounces, disposable emails, and spam traps, and learn how to upgrade your backend with true deliverability validation.
Almost every developer has faced this exact scenario: you are building a new registration feature, you need to secure an input field, and you immediately head over to Stack Overflow to search for the ultimate regex for email validation. You grab the most upvoted snippet, paste it into your codebase, and assume your database is protected.
You scroll through debates about the RFC 5322 standard, copy a massive, unreadable block of characters that looks like someone smashed their keyboard, and paste it into your application. The code works. The form rejects inputs without an "@" symbol. You close the ticket and move on.
But a few weeks later, your marketing team is furious. Their campaigns are failing. They are hitting hard bounces left and right, and your sender reputation is tanking.
You check the database, and the emails look perfectly fine: fakeuser_999@gmail.com or test@mailinator.com. They passed your strict email regex pattern python script flawlessly. So, what went wrong?
The harsh reality of modern development is that syntax validation is not deliverability validation. Relying solely on regular expressions is like checking if a house has a mailbox, but never checking if anyone actually lives inside.
In this guide, we are going to explore the strict limits of email syntax, why up to 40% of invalid emails pass regex checks, and what you must do to truly protect your database.
Key Takeaways (TL;DR)
- Regex is Blind: A regex validation email script only checks the shape of the characters. It cannot verify if the domain is active, if the mail server is online, or if the specific user account exists.
- The 40% Failure Rate: Standard syntax checks let in disposable emails, abandoned inboxes, and spam traps, which account for a massive percentage of B2B and B2C data decay.
- The Bounce Risk: Relying solely on a Syntax Checker guarantees that your application will collect bad data, eventually leading to high bounce rates and IP blacklisting from Google and Yahoo.
- The Solution: True validation requires querying DNS records and performing deep SMTP handshakes, ideally offloaded to a dedicated real-time API.
The "Perfect" Regex (And Why It Is a Myth)
Let’s get this out of the way. If you absolutely must use a regular expression for basic frontend validation (just to ensure the user did not accidentally type a phone number), you should use the standard provided by the HTML5 specification.
Here is the widely accepted, simplified email regex:
JavaScript
/^[a-zA-Z0-9.!#$%&'*+/=?^_`{|}~-]+@[a-zA-Z0-9-]+(?:\.[a-zA-Z0-9-]+)*$/This snippet does exactly what it was designed to do: it ensures there is a local part, an "@" symbol, and a domain part.
However, many developers fall down the rabbit hole trying to write an email address regex python script that adheres 100% to the official RFC 5322 specification. That official regex is thousands of characters long and allows for obscure formats (like IP addresses in brackets or quoted strings) that almost no modern email provider supports.
The truth is, even the most mathematically perfect regex is functionally inadequate for business applications.
The Limits of Syntax: What Regex Misses
When you validate email address python or JavaScript using only regex, you are leaving your front door wide open. Here are the three critical threats that easily bypass any syntax check.
1. Hard Bounces (Dead Accounts)
A user might type john.doe@company.com. This passes the regex instantly. But what if John left the company six months ago and the IT department deleted his account?
Regex cannot talk to the internet. It does not know the account is dead. When your automated system sends a welcome email to that address, you will receive a permanent 550 error. If you collect too many of these, you will ruin your domain's reputation. (You can learn more about managing these errors in our guide to Hard Bounce vs. Soft Bounce).
2. Disposable and Burner Emails
Users who want to bypass your paywall, download a gated whitepaper, or spam your forum will use disposable email addresses.
Addresses like random_user@temp-mail.org or test@10minutemail.com are syntactically perfect. Your Syntax Checker will gladly accept them. But these inboxes self-destruct in minutes, leaving your CRM filled with useless, dead contacts.
3. Spam Traps
Spam traps are the most dangerous entities on the internet. These are valid email addresses created by ISPs (like Yahoo) to catch spammers. They look exactly like real emails (e.g., info@abandoned-domain.com).
Because they are perfectly formatted, your regex will accept them. If you send an email to a pristine trap, your IP could be blacklisted immediately. (Read our full breakdown on identifying and removing Spam Traps).
Why Syntax Validation Hurts Your Sender Reputation
In modern software development, bad data is not just an annoyance; it is a massive financial liability.
When you check email address validity using only regex, you are guaranteeing that a percentage of your outbound emails will fail. Email providers like Gmail and Microsoft monitor your bounce rates relentlessly. If they see that you consistently send messages to non-existent users (because your signup form allowed them through), they will classify your application as a spam operation.
Once your domain reputation drops, even your legitimate transactional emails—like password resets or invoice receipts—will start landing in the spam folder.
The Modern Standard: SMTP and API Validation
If regex is not enough, how do you actually validate email address python scripts or Node.js backends?
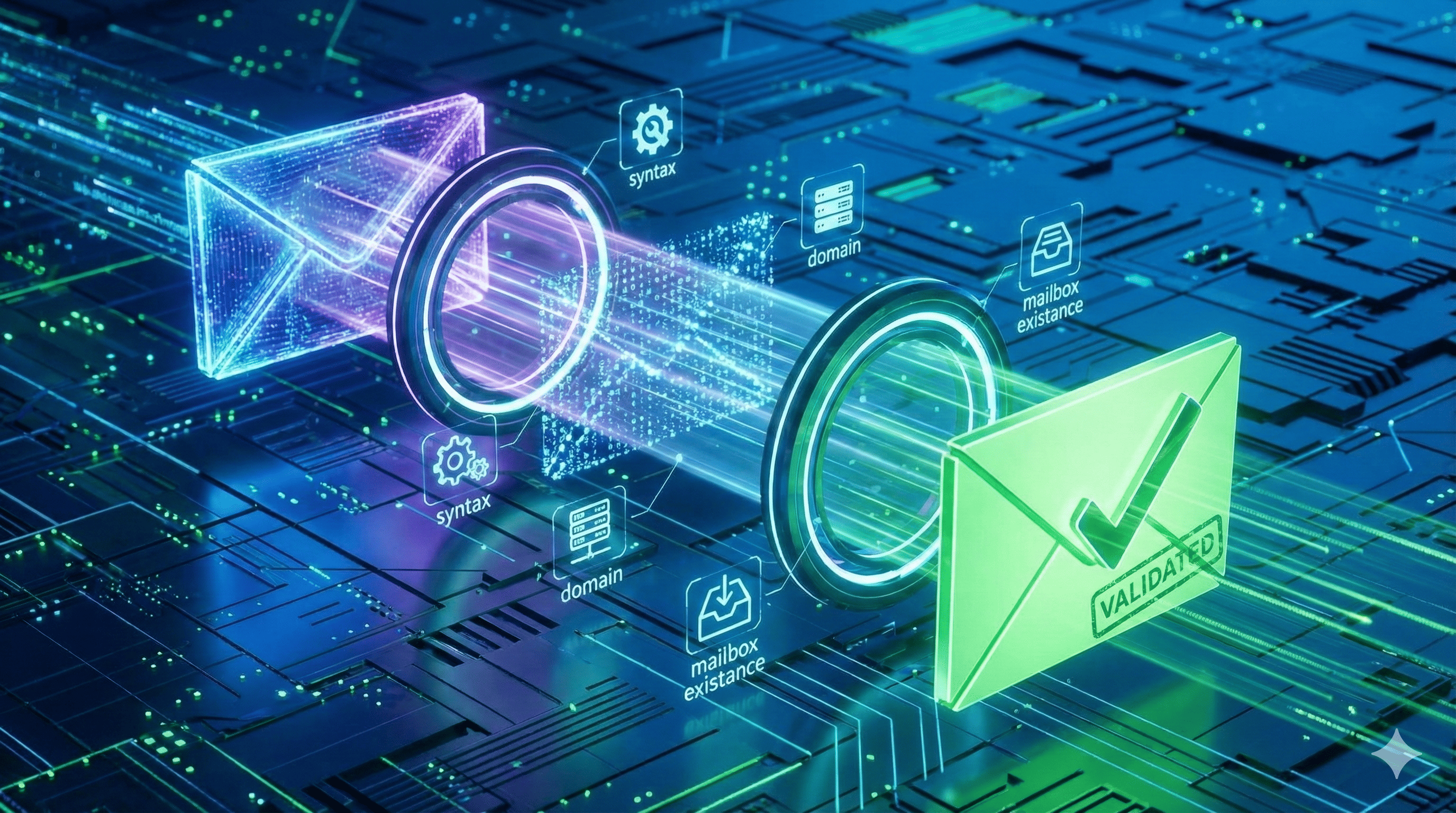
You have to emulate the process of sending an email without actually sending the payload. This involves:
- DNS MX Record Lookups: Checking if the domain actually has mail servers configured to receive traffic.
- SMTP Handshakes: Connecting to the recipient's mail server over port 25 and asking the server directly, "Does this user exist?"
Writing this architecture from scratch is incredibly complex due to greylisting, IP rate limits, and Catch-All servers. If you want to see exactly how this logic is built, check out our deep-dive tutorials on Python Email Validation and building a Node.js Real-Time Checker.
However, the industry standard for production environments is to offload this complexity to a dedicated email validation API. By making a single HTTP request, you can instantly verify syntax, check DNS, perform the SMTP handshake, and cross-reference the domain against real-time disposable email databases.
Conclusion
Regex is a fantastic tool for pattern matching, but it is a terrible tool for verifying reality.
Using regex for email validation is an important first step to catch basic typos on the frontend and save API calls. But it must be treated as exactly that: a first step. To maintain a clean database, protect your sender reputation, and stop burner accounts, your backend must implement deep deliverability validation.
Stop letting fake users pass your filters.
Ready to upgrade your validation logic? Get your API key and 1,000 free requests with EmailAwesome today.
Table of contents
Written by
Frequently Asked Questions
Check the most Frequently Asked Questions
Why is regex insufficient for verifying emails?
What happens if I only use regex for my SaaS signup form?
What steps are required beyond regex syntax checking?
How does SMTP verification beat regex?
Should I completely stop using regex?