Claim & start
< Back to blog
How to Keep Cold Emails Out of Spam: The Ultimate Deliverability Guide
Is your outreach landing in the spam folder? Stop guessing and start fixing. Discover the exact technical guide to authenticate your domain, purge your list of toxic data, and ensure your cold emails hit the primary inbox every time.

The biggest blocker to cold email success isn't a poorly written subject line or a weak call-to-action—it's the spam folder. If your outreach never reaches the primary inbox, your return on investment (ROI) drops to zero.
Mailbox providers (MBPs) like Google Workspace, Microsoft 365, and Yahoo have drastically tightened their security filters. They deploy sophisticated AI to analyze your sending patterns, your infrastructure, and your data quality. It is no longer enough to simply avoid "spammy" words in your copy; you need a flawless technical setup.
In this comprehensive guide, we break down the "Deliverability Trifecta"—Infrastructure, List Hygiene, and Sending Behavior—and provide the exact technical steps required to fix your deliverability for good.
Part 1: The Infrastructure (Locking Down Your Domain)
Before you write your first pitch, you must secure your foundation. Spam filters scan your email's invisible headers to verify your identity. If you fail to meet the strict Google and Yahoo email sender requirements, your messages will be automatically rejected.
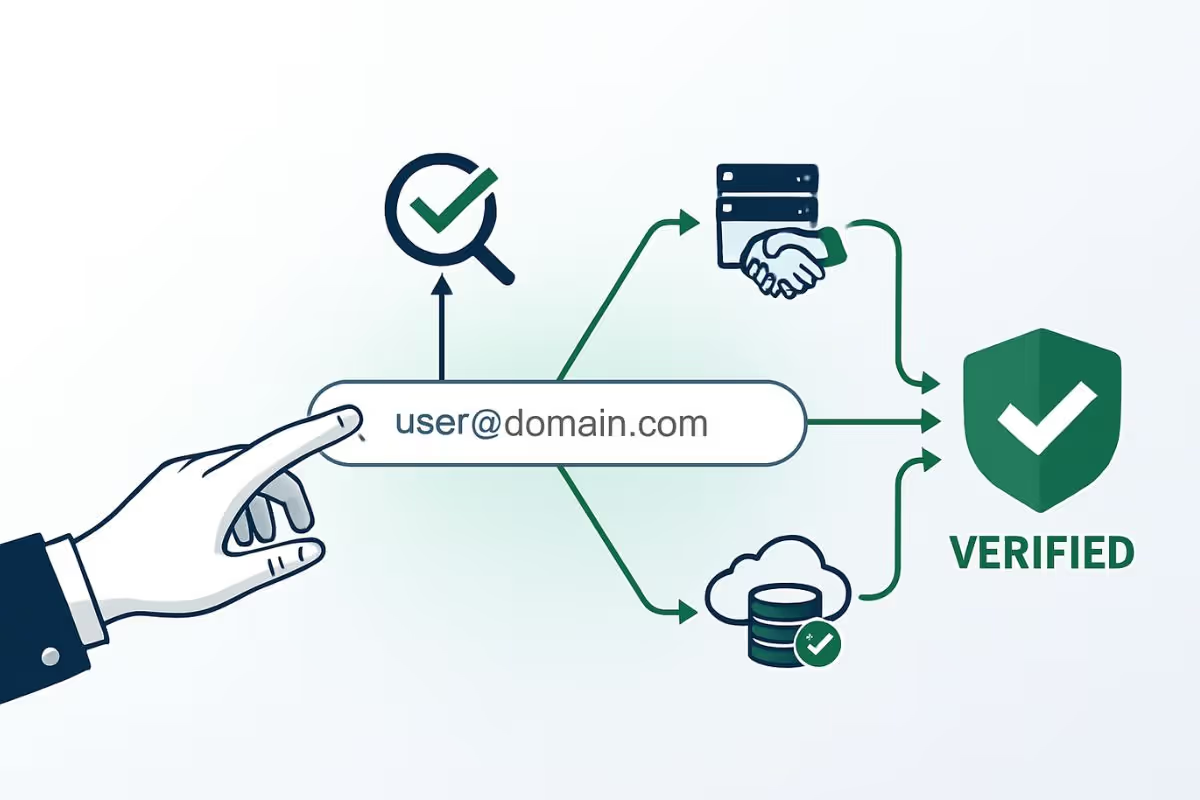
1. Master SPF, DKIM, and DMARC Authentication
These three DNS records are non-negotiable for modern cold emailers.
- SPF (Sender Policy Framework): This acts as a guest list for your domain. It explicitly authorizes your specific sending tools (like Lemlist, Instantly, or Smartlead) to send emails on behalf of your domain.
- DKIM (DomainKeys Identified Mail): This adds a hidden cryptographic signature to your emails. It guarantees the receiving server that the content was not altered or tampered with in transit.
- DMARC: This is the enforcer. It tells receiving servers exactly what to do (reject, quarantine, or do nothing) if an email fails the SPF or DKIM checks. To protect your sender score, you should gradually move your DMARC policy from
p=nonetop=quarantineorp=reject.
2. Set Up a Custom Tracking Domain (CTD)
This is the secret weapon of elite cold emailers. When you use an outreach tool to track open rates and clicks, the tool wraps your links in a tracking URL. By default, you share this tracking domain with thousands of other users on that platform. If one of those users sends spam and gets the shared tracking domain blocklisted, your emails will go to spam too.
By setting up a Custom Tracking Domain (a CNAME record pointing to your outreach tool), you isolate your reputation. Your links will use your own domain (e.g., track.yourcompany.com), completely shielding you from the bad behavior of other senders.
Part 2: List Hygiene (Purging Toxic Data)
Even the most perfectly authenticated email will be heavily penalized if you send it to outdated, fake, or risky addresses. B2B data decays at an average rate of 22% per year. Sending emails blindly to unverified lists is the fastest way to destroy your domain's trust score.
Before launching any campaign, you must process your entire lead list through an advanced email validation API like EmailAwesome. This crucial step protects you against three major threats:
1. Eliminating Hard Bounces
Understanding the difference between a hard bounce and a soft bounce is vital. A hard bounce means the email address no longer exists. If your hard bounce rate climbs above 2%, MBPs will flag you as a spammer who is guessing emails. Deep validation removes these dead ends before you hit send.
2. Dodging Spam Traps
ISPs and blocklist operators (like Spamhaus) use abandoned email addresses as hidden "honeypots" to catch data scrapers and careless senders. Knowing what a spam trap is isn't enough—you cannot spot them with the naked eye. An API cross-references your list against known trap databases to automatically filter them out, protecting you from permanent IP and domain blocklists.
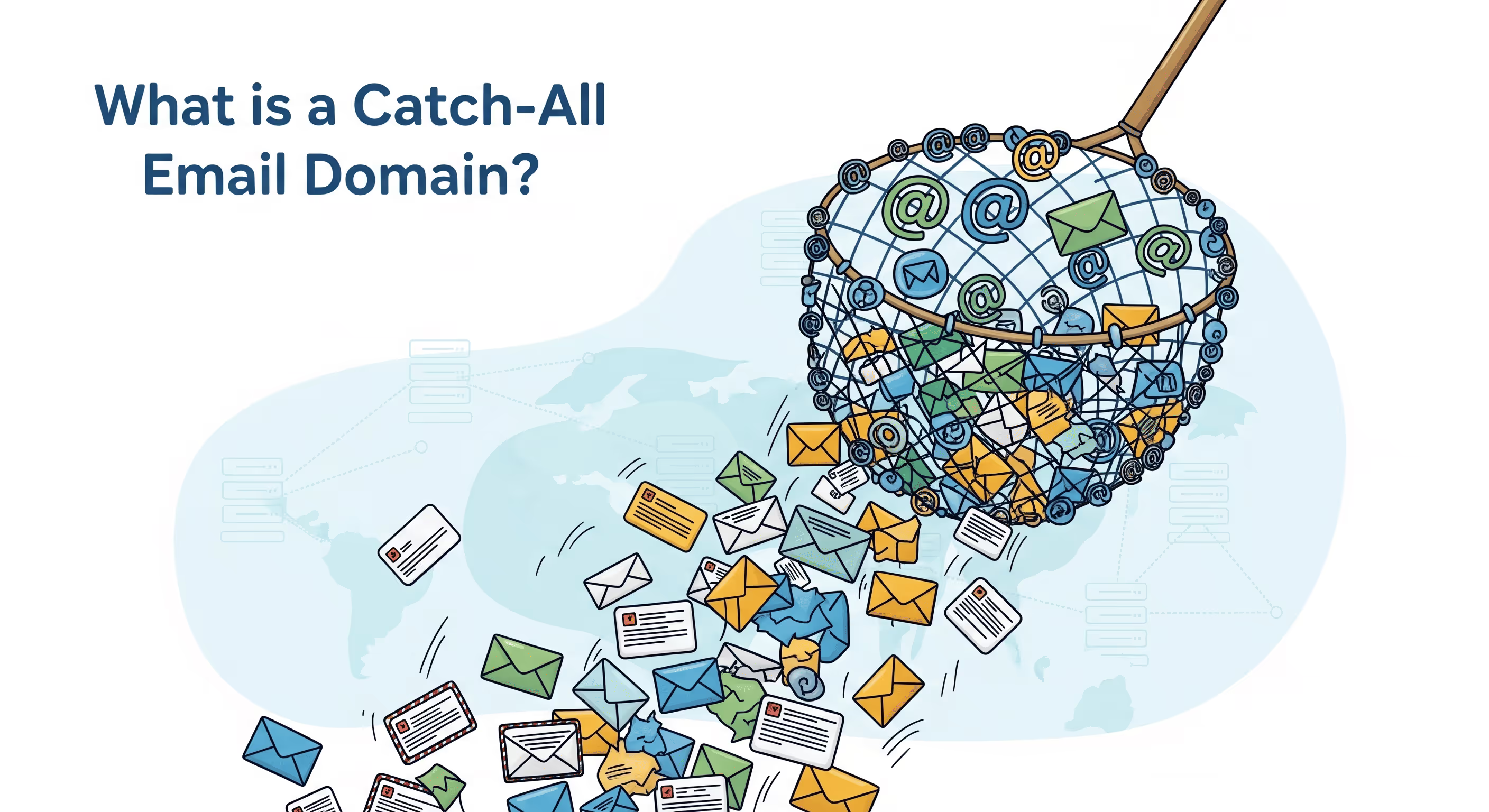
3. Handling Risky Domains
Not all valid emails are safe to send to. An advanced validator will help you identify catch-all email domains and disposable email addresses in your list. Catch-all servers can randomly bounce your emails later, severely hurting your deliverability. By identifying them beforehand, you can segment these high-risk addresses into separate, highly cautious campaigns.
Part 3: Sending Behavior and Content Optimization
Once your infrastructure is secure and your data is clean, you must focus on how you send and what you say. Modern spam filters use AI to analyze your sending volume and the footprint of your email body.
1. Execute a Strict Warm-Up Protocol
You cannot buy a new domain and instantly blast 5,000 emails. Google and Microsoft will instantly throttle or ban your workspace. You must "warm up" your domain over 14 to 21 days. This involves using an automated network to send a small, gradually increasing volume of emails that are automatically opened, replied to, and marked as "not spam." This proves to MBP algorithms that you are a legitimate human sender.
2. Respect Daily Sending Limits
Even after a successful warm-up, pushing your volume too high will trigger spam filters. For a standard Google Workspace or Microsoft 365 account, the golden rule of cold email is to never exceed 30 to 50 cold emails per day, per inbox. If you need to send 500 emails a day, do not use one inbox—purchase 10 separate secondary domains and distribute the load.
3. Use Spintax to Randomize Your Footprint
If you send the exact same email template 1,000 times, Google's AI will recognize the identical text string and flag it as automated bulk spam. To bypass this, elite senders use "Spintax" (Spin Syntax) to dynamically alter greetings, sign-offs, and sentence structures.
- Example:
{Hi|Hello|Hey} {{first_name}}, I noticed your {company|team|agency} is growing.This ensures every single email has a unique HTML footprint, making it look like a manually typed message.
4. Optimize the Text-to-Link Ratio
Too many links in a first-touch cold email look highly suspicious to firewalls. Maintain a healthy ratio: 90% plain text and one link maximum (preferably in your signature). Avoid attaching heavy images, PDFs, or using overly promotional language ("Buy Now," "Exclusive Deal"). If you are targeting highly secure enterprise servers, consider turning off your open-tracking pixels for the first touchpoint, as corporate firewalls often block them.
Part 4: Monitoring and Damage Control
Your domain carries an invisible trust score. You must proactively monitor your health to prevent disasters before they happen.
Use free tools like Google Postmaster Tools or Talos Intelligence to closely track your domain reputation. If you notice a sudden drop in open rates (falling below 30%) or your domain reputation drops from "High" to "Medium" or "Poor," you must pause your outreach immediately.
Continuing to send emails while your score is dropping will result in a permanent block. Instead, you need to follow a strict technical blueprint to fix your email sender reputation, which includes halting all mass campaigns, running a deep data purge with EmailAwesome, and re-entering a controlled warm-up phase.
Table of contents
Written by
Frequently Asked Questions
Check the most Frequently Asked Questions
Is sending cold emails illegal?
Why are my cold emails going to spam if I use plain text and no links?
How often should I validate my cold email list?
Can I use my primary company domain for cold emailing?
Does "Email Warm-up" actually help avoid the spam folder?