Claim & start
< Back to blog
B2B vs. B2C Email Verification: Understanding the Technical Differences
Email verification is not a one-size-fits-all process. Pinging a free Gmail inbox requires an entirely different technical approach than bypassing a strict corporate firewall. Discover the critical differences between B2B and B2C email verification, and learn how to protect your sender reputation from disposable emails, catch-all domains, and massive data decay.

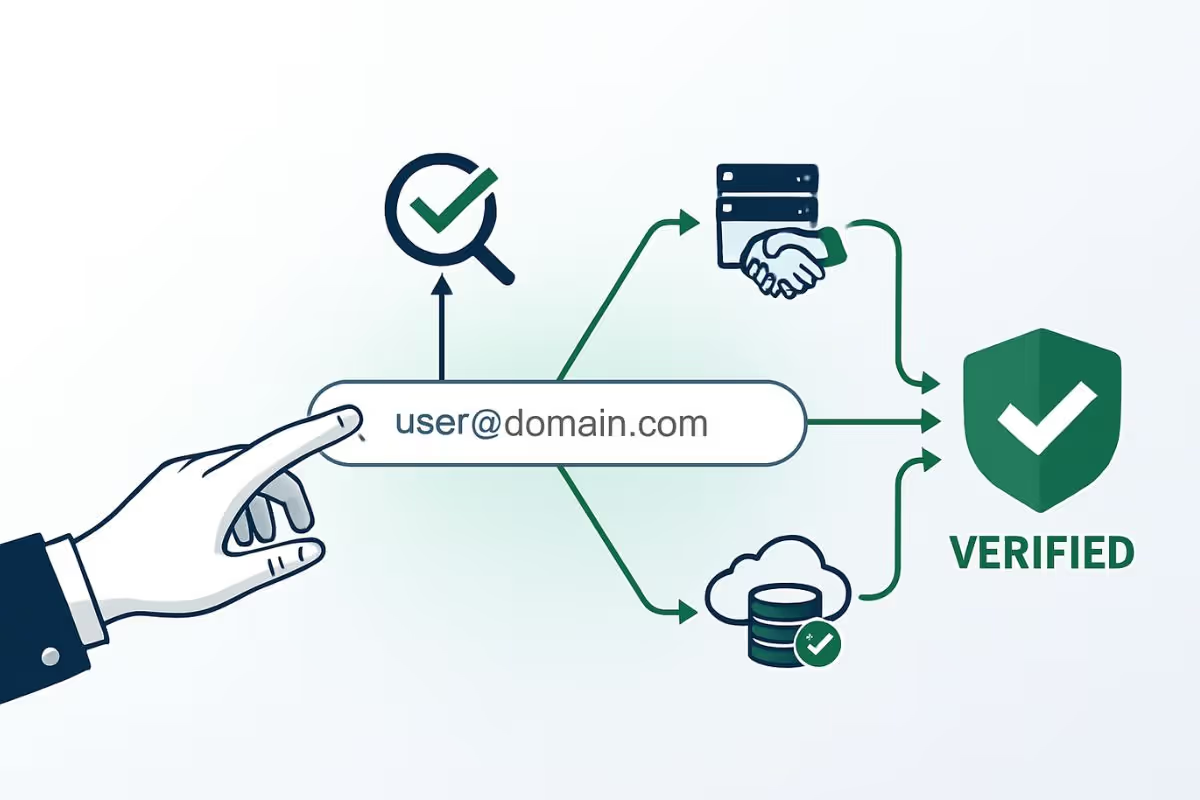
Email verification is widely misunderstood as a simple "yes or no" syntax check. In reality, modern email validation is a complex series of DNS lookups and SMTP handshakes.
More importantly, it is not a one-size-fits-all process. Validating a personal @gmail.com address behaves entirely differently than verifying a corporate @enterprise.com server hidden behind a strict cybersecurity firewall.
If you treat Business-to-Business (B2B) and Business-to-Consumer (B2C) data the same way, you will either block legitimate enterprise customers or allow thousands of fake consumer signups into your database. Understanding the technical differences between B2B and B2C email verification is the key to maintaining a flawless sender reputation.
The B2B Verification Challenge: Corporate Firewalls and Data Decay
When you collect B2B data, you are dealing with corporate infrastructures. These domains are heavily protected, and the lists degrade at an alarming rate. Here is what makes B2B verification so difficult:
1. The 22% Annual Data Decay (Hard Bounces)
Unlike consumers who keep their personal Gmail accounts for decades, B2B professionals change jobs, get promoted, or leave companies frequently. Industry data shows that B2B email lists decay at a rate of 22% per year. If you email a list that is six months old without verifying it, you will generate a massive spike in hard bounces. Understanding the impact of a hard bounce vs soft bounce is critical; exceeding a 2% hard bounce rate will instantly trigger ISP spam filters.
2. The "Catch-All" Server Dilemma
Many B2B organizations configure their mail servers to "accept all" incoming mail to prevent losing important business inquiries due to typos (e.g., routing j.smith@company.com and johnsmith@company.com to the same place).
However, this makes traditional verification nearly impossible. Knowing what a catch-all email domain is is essential. If a standard verifier pings a catch-all server, the server will falsely reply "Yes, this is valid"—even if the employee left the company three years ago. If you send the email, it will silently bounce internally, ruining your deliverability.
3. Role-Based Emails
Addresses like info@, sales@, or admin@ are common in B2B lists. While these are technically valid, sending automated cold outreach to role-based emails often results in high spam complaints because they are monitored by multiple people who did not opt-in.
The B2C Verification Challenge: Scale, Fraud, and Typos
B2C databases grow much faster than B2B lists, usually driven by free trials, e-commerce discounts, or newsletter signups. The challenge here is not corporate firewalls, but human behavior and fraud.
1. The Rise of Disposable Emails
Consumers are highly protective of their primary inboxes. To access a free PDF or a one-time discount code, they frequently use disposable email addresses (like TempMail or 10MinuteMail). These inboxes self-destruct after 10 minutes. If your B2C SaaS platform allows disposable emails, your metrics will be inflated with fake users, and your subsequent marketing emails will hard bounce permanently.
2. High Volume of Typos and Syntax Errors
B2C signups often happen on mobile devices. A user attempting to type john@gmail.com might accidentally type john@gmai.com. Without real-time verification at the point of entry, that typo becomes a dead lead in your CRM.
3. Recycled Spam Traps
Because consumers abandon old Yahoo or AOL accounts, inbox providers often repurpose these dead addresses into honeypots. If you don't know what a spam trap is and you email one of these recycled B2C addresses, your sending IP will be blacklisted globally.
B2B vs B2C: The Technical Breakdown

The Solution: Adaptive Email Verification
The fatal mistake most marketing teams make is relying on basic regex scripts or cheap, outdated verification tools that treat all emails equally. A basic script cannot bypass a B2B anti-spam firewall, nor can it keep up with the thousands of new disposable B2C domains created every day.
Whether you are cleaning a massive B2B cold outreach list or securing your B2C SaaS signup form, you need an adaptive verification infrastructure.
By utilizing an enterprise-grade API like EmailAwesome, your system automatically detects the context of the email.
- If it detects a B2B domain, it deploys advanced SMTP handshakes to safely navigate catch-all configurations without getting blocked.
- If it detects a B2C domain, it instantly cross-references the input against a continuously updated database of disposable and high-risk domains, blocking fake signups in milliseconds.
To comply with the strict Google and Yahoo email sender requirements and ensure your campaigns actually generate revenue, you must adapt your data hygiene strategy. By implementing a professional verification protocol, you eliminate hard bounces, block fraud, and permanently fix your email sender reputation.
Table of contents
Written by
Frequently Asked Questions
Check the most Frequently Asked Questions
Can I use the same verification API for both B2B and B2C lists?
Why do B2B emails take longer to verify than B2C emails?
Should I delete all catch-all emails from my B2B list?
How do I stop disposable emails on my B2C signup form?